Digital Assets
Overview
Digital assets, including cryptocurrencies, stablecoins, tokens, and non-fungible tokens (NFTs), are continuing to gain traction with investors. Millions of people globally, including 16% of adult Americans, have purchased cryptocurrencies, digital tokens, and non-fungible tokens NFTs. These assets are created, stored, and traded on a digital platform, such as a blockchain, and can be bought, sold, or traded like traditional assets.
By 2027, revenue in the Digital Assets segment is projected to reach US$102,700.00m, and the number of users is expected to reach 994.30m (Statista). Cryptocurrencies, specifically, roughly quadrupled in value from the end of 2020 to late 2021, when the market was worth more than $3 trillion (Time Magazine).
Situation & challenge
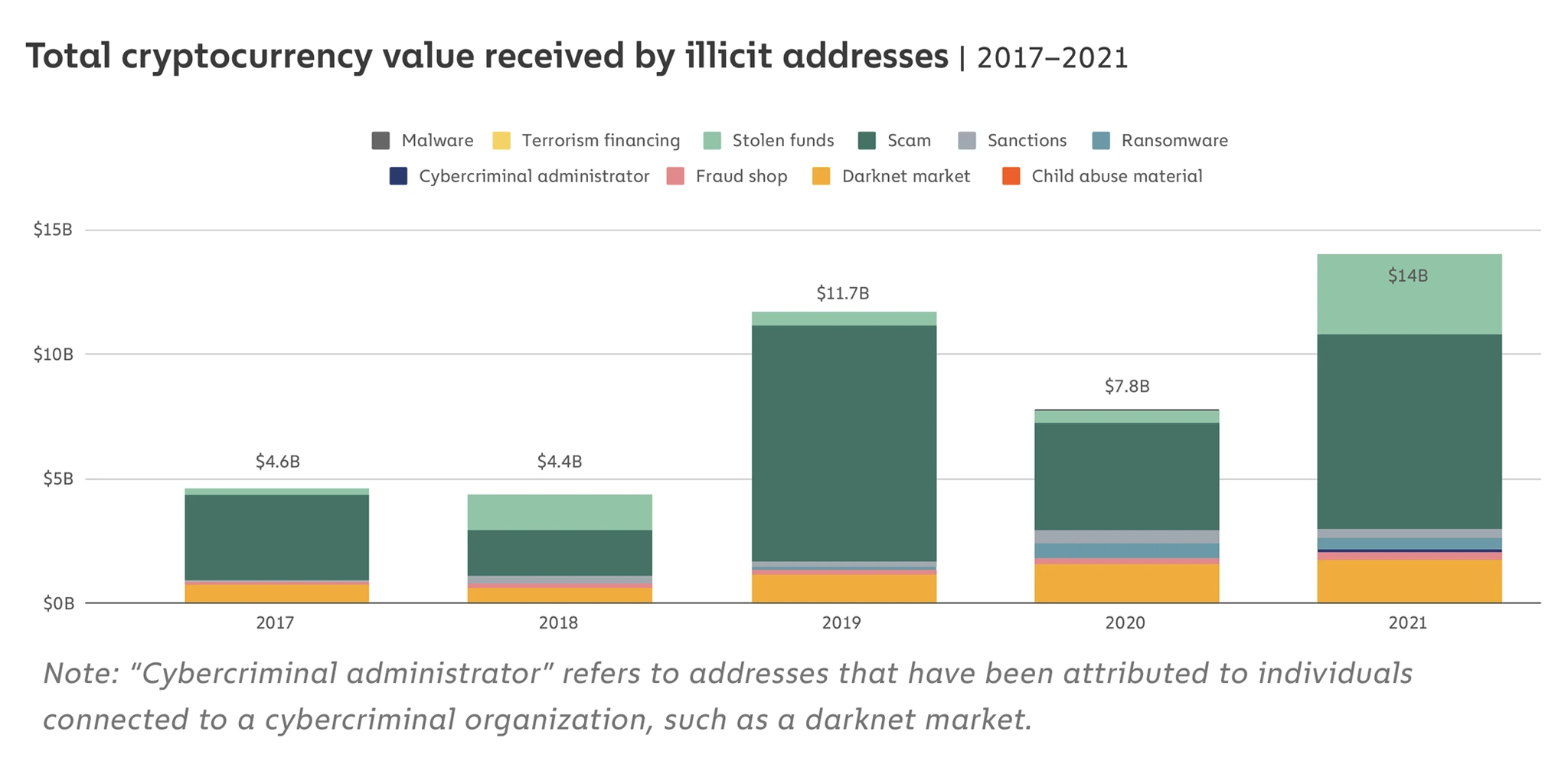
In the digital assets market, crypto frauds remain the biggest form of crime by which asset holders lose funds. Cryptocurrency-based crime hit a new all-time high in 2021, with illicit addresses receiving $14 billion over the course of the year, up from $7.8 billion in 2020 (Chainalysis).
Given the accelerated growth of crypto wallet adoption as well as threats, asset holders must take steps to safeguard their accounts against hacks. DeFi wallets are particularly attractive options for individuals seeking transparency and independence from financial institutions. They come with the onus of self-custody however, and therefore are vulnerable to cyber-attacks.
Wallet owners typically safeguard their accounts by keep their keys or seed phrases (for wallet recovery) in a secure location, either offline, or in local storage on their device, or in cloud storage. They also add two-factor authentication to access their account. But are these measures enough? There is no protection from human error in sending these digital keys to the wrong recipient or just losing them. Once a bad actor has their hands on these keys, they can also call the user’s phone company and convince them to transfer the user’s phone number to theirs. And voila – they have full access to the user’s holdings.
To address these threats, Keyavi integrates with your wallet to fully secure your users’ assets.
Need: Protection against private key/seed phrase theft
Add Keyavi protection to your wallet.
Upon wallet creation, Keyavi’s patented technology infuses protection directly into the private keys/seed phrases, across all its copies, wherever it travels, in perpetuity. Decrypting these keys requires Keyavi authentication – which a hacker will not get.
Need: Easy management of wallet access: who/where/when
Enable policy enforcement at your users’ fingertips
The user can set a geofence and time embargo to manage access to their wallet. They can even authorize access to other users, e.g., a broker to transact on their behalf.
Need: Visibility into their wallet access history
Provide real-time forensics to your users
Every session, every withdrawal transaction, and every wallet recovery is logged. The user has complete visibility into the access history of their wallet, down to the related timestamp and geolocation.

Turn your data into its own fortress
We are establishing a partner ecosystem with best-in-breed industry leaders in wallets and exchanges. With Keyavi as your security backbone, you can focus on driving your business, and time and attention spent on securing your users’ data.
To learn more, contact us at [email protected]